Featured Story
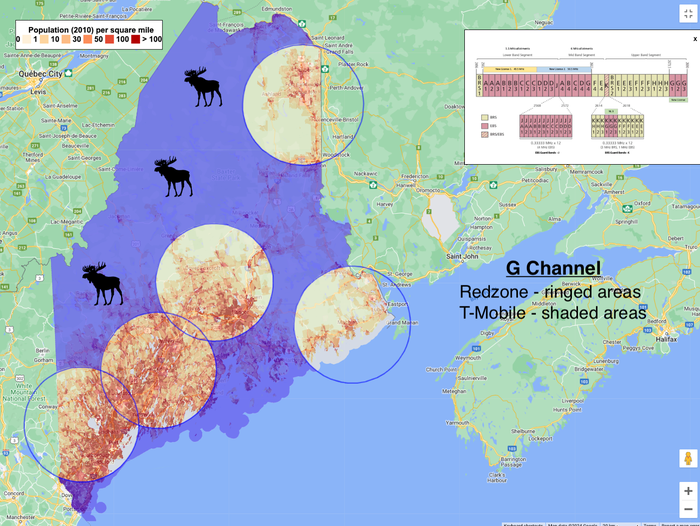
Redzone, NextWave also complain of interference from T-Mobile's 5G
Following a complaint from Bloosurf, NextWave and Redzone said their operations are also suffering interference from T-Mobile's 5G network in 2.5GHz spectrum. Meanwhile, T-Mobile is buying more of it.



























.png?width=700&auto=webp&quality=80&disable=upscale)

.png?width=300&auto=webp&quality=80&disable=upscale)


.png?width=300&auto=webp&quality=80&disable=upscale)
.png?width=300&auto=webp&quality=80&disable=upscale)